As SANS prepares for the 2018 ICS Summit in Orlando, Dean Parsons is preparing a SANS ICS Webcast to precede the event, a Summit talk, and a SANS@Night presentation. In this blog, Dean tackles some common questions about how new or existing industrial control system (ICS) facilities can mature their defense and approach asset identification.
What's an effective defense strategy against the increased volume and sophistication of ICS threats?
Globally, we've passed the point where cyber attackers only target and disrupt information technology networks and business applications. Adversaries have stepped up their attack skills targeting ICS in recent years. However, defense is do-able! Facilities can mature their cybersecurity posture to ensure early detection and protection against these growing threats.
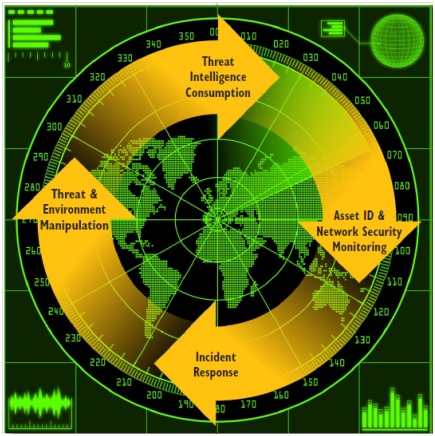
With foundational security already in place, the Active Cyber Defense Cycle (ACDC) empowers ICS defenders to actively hunt for advanced threats in their network, a process which drives informed incident response and quick protective actions.
What is the Active Cyber Defense Cycle?
The different phases of the Active Cyber Defense Cycle support one another to enable proactive security. The four ACDC phases are (1) Asset Identification & Network Security Monitoring, (2) Incident Response, (3) Threat & Environment Manipulation, and (4) Threat Intelligence Consumption. This repeatable process, which requires dedicated assets, involves using and sharing threat intelligence, knowing network layouts and assets, actively hunting for threats, rapidly scoping events of interest, and kicking off containment or protection actions to neutralize threats.
Note that Information Technology and Operations Technology incident response have distinct differences that should be considered throughout the ACDC. These differences involve areas such as the well-being of staff and the protection of physical assets. ICS cybersecurity staff need both a security mindset and a clear understanding of physical processes. They must have solid respect for the safety and reliability of operations while also actively monitoring the network to interpret what is normal and what is not in their ICS. The ACDC has been proven effective in detecting and disarming both Information Technology and ICS-specific threats inside an ICS environment.
When is the right time to adopt the ACDC for active defense for our ICS?
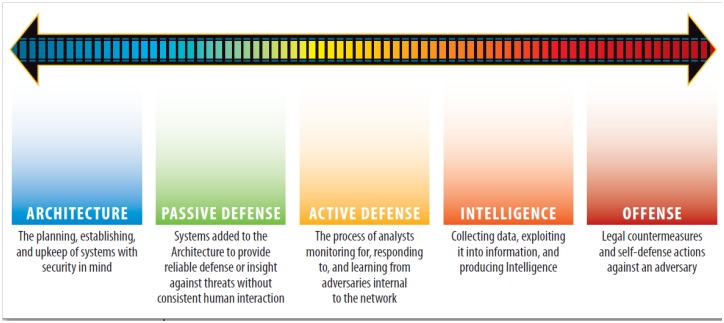
Building on a strong security foundation is key. The phrase "you have to walk before you can run" comes to mind. The Sliding Scale of Cybersecurity is a progressive path upon which ICS facilities can build as they mature their security posture. The first two steps on the scale are Architecture and Passive Defenses. These refer to fundamental security practices such as proper network segmentation, system hardening, patching, and passive defenses including anti-malware, firewalls, and basic intrusion detection technologies. These practices do not require human interaction to function, and they do an adequate job of neutralizing most cyber-criminal and nuisance threats. However, while continuing to defend against these low-impact threats is important, today's threats involve defending against more sophisticated and skilled cyber adversaries. Modern adversary campaigns are designed to penetrate beyond basic defenses and have the potential to exfiltrate sensitive information from an ICS or disrupt physical ICS processes.
An increasing number of facilities, including critical infrastructure (i.e., power grids, transportation systems, oil and gas pipelines, wastewater management systems, etc.), have a good handle on the Sliding Scale of Cybersecurity. Once a facility is mature in Architecture and Passive Defenses the next step on the scale is to have a trained and dedicated team in place to implement and benefit from the Active Cyber Defense Cycle. The team needs deep knowledge of cybersecurity at a tactical level as well as an understanding of physical processes from end-to-end.
Where in the Active Cyber Defense Cycle should we start our defense efforts?
Asset Identification is a great place to start when adopting the ACDC model simply because it's difficult to defend what you don't know you have. If you've seen the movie "The Matrix" you'll remember when Neo visits the Oracle. She shows him a sign in her kitchen that reads "Temet Nosce," which means "Know Thyself." Asset Identification is all about knowing yourself better than the adversary knows you. It's a prerequisite for good network security monitoring and is essential for the other phases of ACDC.
While it seems obvious that maintaining an inventory of assets is critical, it's surprising how many facilities do not regularly keep such an inventory up to date. Not maintaining an asset inventory will come back to bite you in real incident response situations when quick triage and prompt action are needed to support safe and reliable operations. For example, when consuming threat intelligence, it is critical to know the vendor, model number, firmware versions, and patch levels plays in order to understand your internal risk surface, which is what drives your defense efforts to implement compensatory controls, network changes, and/or additional monitoring in weak areas. With an updated asset inventory and an ACDC in place, you are already a step ahead of the adversary.
What are some approaches to Asset Identification and tracking in performing active defense?
There are four effective Asset Identification methodologies: Physical Inspection, Passive Scanning, Active Scanning, and Configuration Analysis. I've seen solid success with physical inspection, which involves physically walking (and, if you have to, crawling) through your facilities to record asset information and update network diagrams and as-built documentation. These on-site visits provide face-to-face time for security awareness discussions and other opportunities that are not practical by other means such as remote access or email or phone. This approach lends itself well to building the effective relationships between Information Technology and Operations Technology teams that are necessary for smooth ICS incident response. These engagements provide talking points on how new Operations Technology asset installations or upgrades may have been completed in a manner different than what had been planned on paper, which could have introduced security gaps.
In ICS facilities, safety is always a concern. So when going on-site, personal protective equipment such as hard hats, safety glasses, visible safety vests, steal-toe boots, and ear protection will be required in designated zones. So coordinate your planning with the safety department and leaders on-site, grab your personal protective equipment and a spreadsheet app, and undertake what will be a very informative and beneficial exercise. Embrace the safety culture and model a "cyber" safety culture to match and support physical safety.
Once you're back at the office you'll want to handle the inventory information carefully. It is good practice to enter information into a database that's scalable and secured in an isolated area with appropriate strong authentication and change control. Making the database easily searchable will streamline analysis when consuming the next round of threat intelligence to evaluate your internal risk surface. Once the inventory is recorded it should be maintained. To get ahead of changes and to be ready for new assets that come in, be sure to have security requirements in scope for projects on asset and software selection, and change management.
As long as there are ICS adversaries, the job of defending ICS never ends, and neither does the Active Cyber Defense Cycle. Starting with asset identification to know yourself better than your adversary is critical to active defense. The ACDC and other key ICS strategic defense topics, including numerous case studies and hands-on labs, are covered in depth in SANS ICS515: ICS Active Defense and Incident Response.
Dean's upcoming talks:
- Canadian Webcast Series, Part 3: "ICS Defense: It's Not a 'Copy-Paste' from an IT Playbook."
- ICS Summit Talk: "Adventures in ICS Asset Identification: Physical Inspection Style." Tuesday, March 20, 2:30-3:15 pm - ICS Summit Orlando, FL.
- ICS SANS@Night: "Learning from the Adversary: The Value of Malware Analysis for ICS." Thursday, March 22, 6:00-7:00pm - ICS Summit Orlando, FL.
- See Upcoming SANS ICS Summit and SANS ICS515 Training Opportunities
- Earn the GRID certification to actively defend and respond to ICS cyber attacks.
- Join the SANS Community ICS Forum and be part of the conversation where 4,000+ ICS professionals share, discuss, and ask questions about ICS-related issues.
To view all our upcoming courses and events, click here. Available live or OnDemand.
Free Stuff Reminder
- Download the "What Will Your Attack Look Like" poster here
- Get the latest ICS resources here
- Join the conversation in the ICS Community Forum where ICS professionals share lessons learned, ask questions and connect with others passionate about securing our critical infrastructure.